There is a quiet shift happening in telecom right now, and most providers (ITSPs, CSPs and MSPs) have not adjusted to it. Compliance is still widely treated as a regulatory obligation, something to revisit when rules change, or audits require it. However, that framing no longer reflects reality. Today, compliance plays a direct role in whether communications actually work. It determines whether calls connect, messages are delivered, and customers can be reached at all.
This shift is being driven by two forces: scale and enforcement.
According to YouMail, Americans continue to receive tens of billions of robocalls annually, forcing carriers and device manufacturers to aggressively filter and label traffic.
At the same time, the Federal Communications Commission has introduced and expanded requirements that fundamentally change how providers operate, including:
- Mandatory STIR/SHAKEN call authentication
- Expanded Do Not Originate (DNO) blocking requirements
- Enforcement of messaging frameworks like 10DLC
- Emergency compliance under RAY BAUM’S Act and Kari’s Law
Together, these forces have reshaped the network.
From Pass-Through to Decision Engine
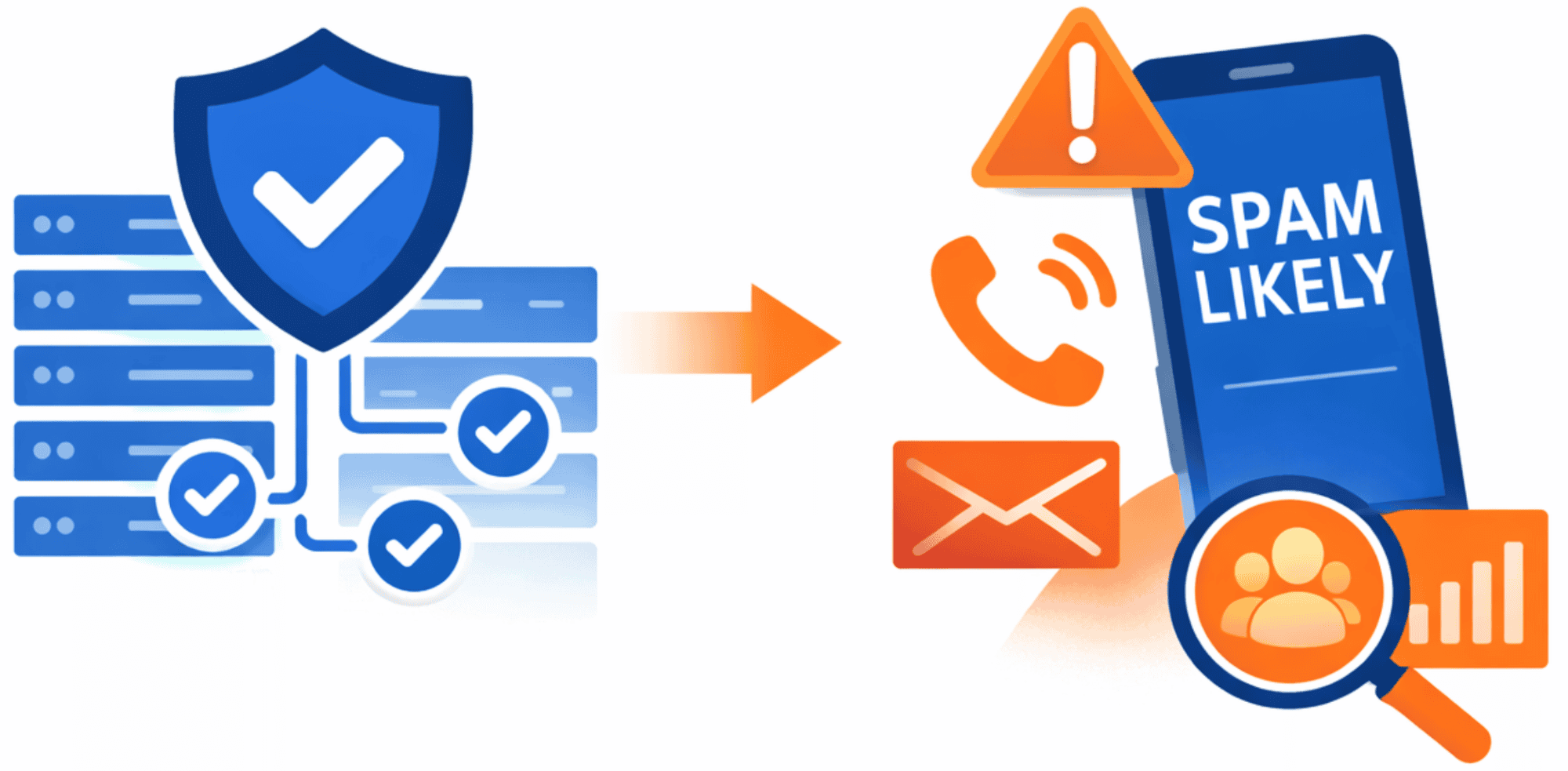
Telecom networks used to do one thing exceptionally well: connect calls. Today, they do something else first, they evaluate them.
Before a call or message reaches the end user, it is assessed in real time based on multiple signals:
- Identity (who is calling)
- Validity (should this call exist)
- Reputation (has this number behaved legitimately)
- Behavior (does the traffic pattern look normal)
Based on that assessment, the network determines whether to deliver the call normally, label it (for example, “Spam Likely”), filter it, or block it entirely.
Analytics firms like Hiya report that a growing percentage of unknown calls are now flagged or blocked, reinforcing how aggressive these decision systems have become.
Why “Compliant” Doesn’t Mean “Effective”
This is where the industry is getting tripped up.
Many providers have done what was required. They’ve implemented STIR/SHAKEN, aligned with regulatory expectations, and assumed that was enough. But STIR/SHAKEN only verifies identity; it does not determine how a call is treated downstream.
That decision is influenced by factors such as caller reputation, historical trust signals, and carrier analytics. As a result, fully compliant organizations are still seeing calls labeled as spam, reduced answer rates, and messages filtered or delayed.
Compliance ensures eligibility. It does not guarantee performance.
The Compliance Stack Has Expanded Whether You Like It or Not
What has emerged is not a single requirement, but a layered system that providers must navigate.
At a high level, today’s telecom compliance environment includes:
- Call Authentication (STIR/SHAKEN)
Required to verify caller identity and prevent spoofing - Call Validation (DNO)
Blocking invalid, unallocated, or fraudulent numbers across the call path - Messaging Compliance (10DLC)
Required registration for A2P messaging to ensure deliverability - Emergency Compliance (E911)
Accurate, dispatchable location data for emergency calls - Fraud & Robocall Mitigation
Detection of suspicious traffic patterns and abuse - Tax & Regulatory Compliance
Accurate billing, rating, and remittance across jurisdictions - Caller ID Reputation (Critical Layer)
Determines how calls are actually perceived and treated
Each of these serves a different purpose. But the network evaluates them together.
This isn’t theoretical. Enforcement is already happening. The FCC has proposed multi-million-dollar fines against providers for failing to properly manage robocall mitigation and caller authentication, including penalties of $4.49 million against a single provider for compliance failures and $2 million for improper caller ID handling. In some cases, fines can reach $10,000 per violation for inaccurate filings or failure to meet reporting requirements
The FCC has already taken action to remove over 1,200 non-compliant providers from the ecosystem, effectively cutting off their ability to operate within the network until compliance is restored.
The Cost of Treating This Like a Checklist
Most providers are not ignoring these requirements, they are addressing them incrementally. The issue is that solving one layer does not solve the system.
A provider can:
- Authenticate calls and still be labeled as spam
- Register messaging and still face delivery issues
- Implement fraud controls and still see declining answer rates
Since the network evaluates all signals collectively, any weakness can influence the outcome.
The impact shows up directly in business performance: missed sales opportunities, lower campaign ROI, reduced customer engagement, and increased operational friction. Even modest improvements in trust signals can have measurable effects. In some cases, improving caller ID reputation alone can increase answer rates by up to 30%, highlighting how tightly delivery and performance are now connected.
Why This Is Getting Harder to Manage Internally
Regulations continue to evolve, enforcement is tightening, and analytics systems are becoming more sophisticated.
Maintaining compliance now requires:
- Continuous monitoring
- Ongoing updates
- Regulatory awareness
- Real-time visibility into network behavior
For many providers, this introduces a level of operational complexity that is difficult to manage with internal tools and fragmented solutions.
A Shift Toward Integrated Compliance
As a result, leading providers are moving away from piecing together individual solutions and toward more integrated approaches. Instead of managing compliance as a series of disconnected tasks, they are treating it as a system that needs to be monitored, maintained, and optimized continuously.
The goal is to meet requirements and ensure that communications perform reliably within the conditions those requirements have created.
Where Sangoma Carrier Voice Fits
Sangoma’s Carrier Voice is built around this exact challenge. Rather than addressing individual compliance requirements in isolation, it provides a unified layer that supports both compliance and performance across the network.
This includes:
- Fully managed STIR/SHAKEN call authentication
- Integrated DNO validation services
- Caller ID monitoring and remediation to improve reputation
- Real-time fraud and robocall detection
- Simplified 10DLC registration for messaging
- E911 dynamic location routing
- Automated tax compliance capabilities
Want the Full Breakdown?
If you are an ITSP, CSP or MSP and want a deeper look at what’s required today, where providers are most exposed and how to simplify compliance without complexity:
-> Download our Free Telecom Compliance Toolkit
By bringing these elements together, Carrier Voice reduces operational burden while improving visibility and control over how communications are handled.
This Isn’t Just Compliance, It’s Connectivity
Telecom compliance has moved from the background to the center of how networks operate. It now determines not just whether providers meet requirements, but whether their communications are trusted, delivered, and acted upon.
Providers that continue to treat compliance as a checklist will struggle to keep up with this shift. Those that approach it as a system, one that connects compliance with performance will be better positioned to maintain reliability, protect customer trust, and drive long-term growth.
Still Unsure Where You Stand?
Get a clear view of your compliance gaps and call performance risks.